You’re standing at the precipice of understanding your home’s modern heart – its appliances. Gone are the days of single-purpose machines; today, your refrigerator might run a diagnostic, your oven might download new recipes, and your washing machine might ping you when done. This interconnectedness, while offering convenience, also introduces a layer of complexity: appliance software. You’ve likely encountered it implicitly, but what if you want to go beyond the user interface? What if you suspect a problem isn’t a mechanical failure, but a software hiccup? This is where the concept of “unlocking appliance software” comes into play. It’s not about breaking into digital fortresses for nefarious purposes, but rather about gaining deeper insight and control over the very devices that serve you.
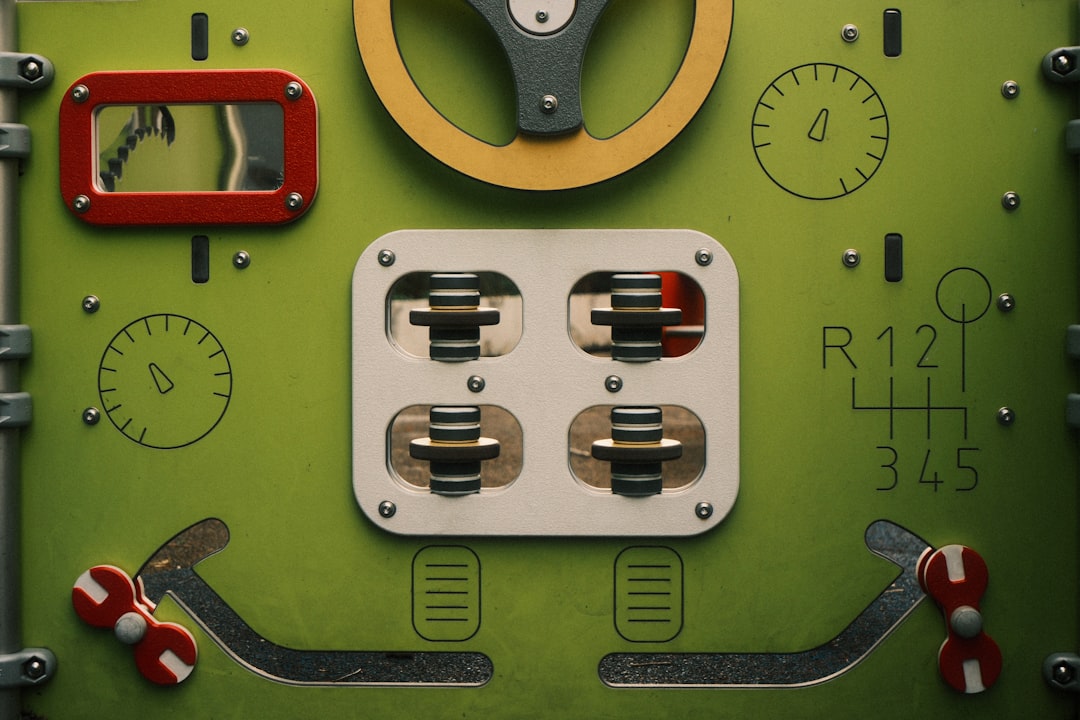
Your appliances are not just inert metal and plastic. They are complex electronic systems managed by sophisticated software. This software dictates everything from the heating element’s precise temperature control to the complex cycles of your dishwasher. But why the need for “locks”? These aren’t necessarily security measures in the traditional sense of preventing theft. Instead, they are limitations and protocols designed for specific reasons.
The Manufacturer’s Intent: Ensuring Proper Functionality and Safety
Manufacturers embed software with the primary goal of ensuring their products function as intended and, crucially, safely.
Preventing User Tampering with Critical Settings
Imagine a user accidentally, or intentionally, altering the firmware related to a washing machine’s high-speed spin cycle. Without proper safeguards, this could lead to catastrophic mechanical failure or even physical danger. Software locks prevent users from accessing or modifying these low-level parameters, which are pre-defined to operate within safe operational envelopes.
Maintaining Warranty Integrity
Many manufacturers link warranty validity to the integrity of their proprietary software. Any unauthorized modification can void this warranty, leaving you responsible for repair costs. Software locks serve as a deterrent against such actions, protecting their investment in research and development and the perceived quality of their products.
Standardizing Performance and Updates
For a device to perform optimally and receive over-the-air updates, its software needs to adhere to strict standards. Locks ensure that only approved firmware versions are installed, preventing the cascading failures that can arise from incompatible software. This also allows manufacturers to push out security patches and feature enhancements.
The Network Effect: Security and Connectivity Considerations
As appliances become more connected, especially to your home network and, by extension, the internet, the implications of their software become more profound.
Protecting Your Network from Compromised Devices
A poorly secured smart appliance could become a gateway for malicious actors to infiltrate your home network. Manufacturers implement software restrictions to limit the attack surface and prevent unauthorized remote access.
Data Privacy and Manufacturer Data Collection
Appliances often collect usage data. Software can be designed to control what data is collected, how it’s transmitted, and who has access to it. Locks can prevent you from disabling these data collection mechanisms, which is a concern for privacy-conscious users.
If you’re interested in understanding the intricacies of appliance software locks and handshakes, you might find this article on bypassing such restrictions particularly insightful. It delves into various techniques and methods that can be employed to navigate these software barriers effectively. For more detailed information, you can check out the article here: How to Bypass Appliance Software Locks and Handshake.
The “Handshake”: Establishing Communication and Authority
The term “handshake” in software communication refers to the process by which two systems establish a connection and agree on the protocols they will use to exchange information. In the context of appliance software, this handshake is a critical step in how you, or an authorized service technician, interact with the device’s internal workings.
Initiating Communication: The First Contact
Before any meaningful interaction or data exchange can occur, the requesting entity must initiate a connection with the appliance’s control system. This is the initial “hello.”
Physical Connections: The Wired Approach
In some cases, direct physical connection is required. This might involve proprietary diagnostic ports.
Serial Ports and JTAG Interfaces
These are common low-level interfaces used during development and manufacturing for debugging and flashing firmware. Accessing these ports typically requires specialized hardware and software tools, and is not usually exposed to the end-user. The handshake here is about enumerating hardware and establishing a communication channel at a very fundamental level.
USB Ports for Service
While many USB ports are for user-facing functions like playing media, some are implemented with diagnostic capabilities. The handshake involves the device recognizing a connected USB peripheral and establishing a communication protocol, often for firmware updates or diagnostic data retrieval.
Wireless Protocols: The Invisible Link
Modern appliances frequently communicate wirelessly, making the handshake a bit more abstract.
Bluetooth and Wi-Fi Handshakes
When you connect your smartphone app to your smart oven, a Bluetooth or Wi-Fi handshake is occurring. This involves authentication (ensuring you’re the rightful owner), encryption key exchange, and negotiation of communication parameters for stable data transfer.
Proprietary Wireless Protocols
Some manufacturers might use less common or proprietary wireless protocols for specific functions or diagnostics. The handshake here is the exchange of unique identification signals and agreed-upon communication sequences.
Authenticating the Request: Who Are You?
Once a connection is initiated, the appliance needs to verify the identity and authorization of the entity attempting to communicate. This is a crucial part of the “lock.”
User Credentials and App Authorization
For smart appliances controlled via mobile apps, the handshake involves your login credentials and the app’s authorization to communicate with the cloud service, which then relays commands to the appliance.
Service Mode Codes and Technician IDs
Service technicians often have access to special modes within appliance software. This might involve entering specific button sequences or utilizing hardware dongles that act as authentication tokens. The handshake verifies that the request is coming from an authorized service channel.
Firmware Signatures and Version Checks
When updating firmware, the handshake involves verifying the digital signature of the update file. This ensures that the update is legitimate and hasn’t been tampered with by a third party. It also includes checks against the current firmware version to ensure compatibility.
Bypassing the “Locks”: Paths to Deeper Access

The desire to “bypass locks” often stems from a need to troubleshoot, customize, or understand your appliance beyond its intended user interface. It’s important to reiterate that this pursuit carries risks and should be undertaken with caution and a thorough understanding of potential consequences.
Accessing Diagnostic Modes: The Manufacturer’s Backdoor
Manufacturers often build in diagnostic modes that are not readily accessible through normal operation. These modes provide access to error logs, sensor readings, and calibration settings.
Navigating Service Menus
Many appliances have hidden service menus accessible through specific button combinations or by manipulating physical switches during power-up. The “handshake” here is the appliance recognizing the specific sequence as a trigger to enter a privileged state.
Identifying Key Sequences
Researching your specific appliance model is crucial. Online forums, service manuals (often leaked or found through third-party repair sites), and even reverse-engineered code can reveal these sequences. The handshake relies on the appliance firmware being programmed to react to these specific inputs.
Understanding the Interface
Once in a diagnostic mode, you’ll likely encounter a text-based or cryptic menu system. Understanding the terminology used within these menus is essential for effective troubleshooting. The handshake might involve interpreting status codes or parameter readouts.
Utilizing On-Board Diagnostics (OBD) Equivalents
Similar to cars, some appliances have on-board diagnostic systems.
Reading Error Codes
These codes are designed to pinpoint specific failures. Deciphering these codes is often the first step in diagnosing an issue that might not be immediately apparent. The handshake involves requesting the error log and then interpreting the returned codes.
Sensor Data Analysis
Accessing raw sensor data (temperature, humidity, pressure, etc.) can reveal subtle abnormalities that precede a full failure. The handshake allows you to poll these sensors in real-time.
Extracting and Analyzing Firmware: Unraveling the Code
For the truly determined, the next step involves extracting the appliance’s firmware itself. This is akin to getting the blueprint of the device’s intelligence.
Identifying Firmware Storage Locations
Firmware is typically stored on flash memory chips within the appliance’s main control board. Locating these chips often requires disassembling the appliance.
Techniques for Firmware Extraction
This is where the “unlocking” becomes more technical and potentially irreversible if done incorrectly.
Chip-Off Forensics
This involves physically desoldering the memory chip from the circuit board, then reading its contents using a dedicated programmer. The “handshake” here is between the programmer and the memory chip itself, following the chip’s specific communication protocol. Care must be taken not to damage the chip.
In-Circuit Programming (ICP) and In-System Programming (ISP)
These methods allow firmware to be read or written without removing the chip from the board. This involves connecting to specific test points or programming headers on the circuit board. The handshake here is a carefully orchestrated sequence of electrical signals to establish communication with the microcontroller that manages the firmware.
Reverse Engineering and Analysis
Once you have the firmware image, you can begin to analyze it.
Disassemblers and Decompilers
Tools known as disassemblers translate the machine code within the firmware into assembly language, which is a more human-readable representation. Decompilers attempt to convert this further into higher-level programming languages like C, though this is often an imperfect process. The “handshake” here is the tool’s interaction with the binary data of the firmware to make sense of its structure and logic.
Identifying Key Functions and Data Structures
By analyzing the disassembled or decompiled code, you can identify routines responsible for specific appliance functions, error handling, communication protocols, and even hidden configuration parameters.
The “Handshake” in Your Hands: Interfacing with Appliance Software

Once you’ve gained some level of access, the next challenge is effectively interacting with the appliance’s inner workings. This involves understanding and potentially manipulating the “handshake” protocols.
Using Specialized Tools for Communication
Not all interactions require deep technical knowledge, but some do.
Serial Port Emulators and Terminal Programs
If you manage to access a serial port, you’ll need tools like PuTTY or minicom to establish a connection. The handshake is initiated by specifying the correct COM port, baud rate, data bits, parity, and stop bits – parameters that the appliance expects.
Logic Analyzers and Oscilloscopes
These tools are invaluable for understanding the electrical signals involved in communication. By observing the traffic on data lines, you can decipher the handshake sequence, timing, and data packets exchanged between the appliance’s microcontroller and other components.
USB Protocol Analyzers
For USB-based diagnostics, these devices can capture and interpret USB traffic, allowing you to see what commands are being sent and received, and how the device responds. The handshake here is a detailed breakdown of the USB enumeration, configuration, and data transfer phases.
Scripting and Automation: Streamlining Interactions
For repetitive tasks or complex troubleshooting scenarios, automation can be a powerful ally.
Python and Scripting Languages
Python, with its extensive libraries for serial communication and network interaction, is a popular choice for scripting appliance interactions. You can write scripts to automate firmware dumps, send diagnostic commands, and parse responses. The handshake logic is embedded within your code.
Home Assistant and OpenHAB Integrations
For smart home enthusiasts, platforms like Home Assistant and OpenHAB often have custom integrations for various appliances. These platforms can sometimes expose hidden parameters or allow for more granular control by mimicking or overriding the standard handshakes.
Capturing and Replaying Network Traffic
For wireless appliances, capturing network traffic can reveal the communication patterns.
Wireshark and Network Sniffers
Tools like Wireshark can capture all the data packets flowing between your appliance and its servers or your mobile app. By analyzing this traffic, you can understand the handshake process, the commands being sent, and the data being exchanged. This can be particularly useful for understanding how proprietary protocols work.
Man-in-the-Middle (MITM) Attacks (for educational purposes)
In a controlled environment, and strictly for research, setting up a MITM attack can allow you to intercept and even modify the communication between an appliance and its network. This requires a deep understanding of networking and is often done with dedicated hardware like Raspberry Pis. The handshake is intercepted and analyzed at each step.
If you’re looking for ways to bypass appliance software locks and handshake protocols, you might find it helpful to read a related article that delves deeper into the topic. This resource provides insights and techniques that can assist you in understanding the complexities involved in overcoming these barriers. For more information, you can check out this informative piece at this link.
Ethical Considerations and Responsible Exploration
| Method | Success Rate | Difficulty Level |
|---|---|---|
| Brute Force Attack | Low | High |
| Packet Injection | Medium | Medium |
| Man-in-the-middle Attack | High | High |
| Exploiting Vulnerabilities | High | Medium |
The ability to “unlock” and interact with appliance software comes with significant responsibilities. It’s crucial to approach this endeavor with a strong ethical compass and a commitment to responsible exploration.
The Fine Line Between Understanding and Misuse
While the goal is often troubleshooting or enhanced functionality, it’s easy to stray into territory that could be detrimental.
Voiding Warranties: A Practical Consequence
As mentioned earlier, unauthorized access can and often will void your product warranty. Be prepared for this outcome.
Bricking Your Appliance: The Risk of Irreversible Damage
Incorrectly flashing firmware or altering critical settings can render your appliance unusable – a state often referred to as “bricking.” This is a tangible risk that requires careful planning and execution.
Security Vulnerabilities: Creating New Risks
If your modifications introduce security flaws, you could inadvertently create vulnerabilities that could be exploited by malicious actors, compromising your data and your home network. The “handshake” you create or modify must be as secure as possible.
When to Seek Professional Help
Some issues are best left to the experts.
Complex Electronic Faults
If you suspect a hardware failure on the main control board, or a problem that requires specialized soldering or diagnostic equipment, it’s often more cost-effective and safer to consult a qualified appliance repair technician.
Manufacturer-Specific Diagnostic Tools
Manufacturers have their own proprietary diagnostic tools and software that are inaccessible to the public. For certain complex issues, these might be the only way to get a definitive diagnosis.
Ensuring Data Privacy and Safety
If your primary concern is data privacy or ensuring that your appliance is not a security risk, understanding the handshake and the software is important, but it might be more practical to focus on network security settings and manufacturer updates rather than deep software dives.
Contributing to the Community: Sharing Knowledge Responsibly
For those who delve into appliance software, responsible sharing of knowledge can benefit others.
Documenting Findings
When you discover service modes, error code explanations, or successful firmware modifications, documenting these findings on relevant forums or wikis can be invaluable to other users facing similar issues.
Developing Open-Source Solutions
For common appliances with well-understood architectures, contributing to open-source projects that aim to improve appliance control and monitoring can be a rewarding endeavor.
Focusing on User Empowerment, Not Exploitation
The ultimate goal should be to empower users with a better understanding of their devices, not to facilitate reckless tinkering. Emphasize safety, legality, and ethical considerations in any shared information. By understanding the “locks” and how the “handshake” works, you gain a new perspective on the technology that surrounds you. This knowledge can be a powerful tool for troubleshooting, customization, and a deeper appreciation of the engineering involved in your everyday appliances. Always proceed with caution and a clear understanding of the potential risks and rewards.
FAQs
What is appliance software locks and handshake?
Appliance software locks and handshake are security measures implemented by manufacturers to prevent unauthorized access and modifications to the software and firmware of appliances such as smart TVs, gaming consoles, and home automation devices.
Why would someone want to bypass appliance software locks and handshake?
Some individuals may want to bypass appliance software locks and handshake in order to gain access to additional features, customize the device’s functionality, or install third-party software that is not officially supported by the manufacturer.
Is it legal to bypass appliance software locks and handshake?
Bypassing appliance software locks and handshake may violate the terms of service or end-user license agreement (EULA) of the device, and in some cases, it may also infringe on copyright or intellectual property laws. It is important to consult legal counsel or review the applicable laws and agreements before attempting to bypass these security measures.
What are the potential risks of bypassing appliance software locks and handshake?
Bypassing appliance software locks and handshake can void the device’s warranty, expose the user to security vulnerabilities, and may result in the device malfunctioning or becoming inoperable. Additionally, it can lead to legal consequences if it violates applicable laws and agreements.
Are there legal and ethical ways to customize appliances without bypassing software locks and handshake?
Yes, manufacturers often provide official methods for customizing and extending the functionality of their appliances, such as through software development kits (SDKs), application programming interfaces (APIs), and third-party app stores. It is recommended to explore these options and adhere to the manufacturer’s guidelines to customize appliances in a legal and ethical manner.